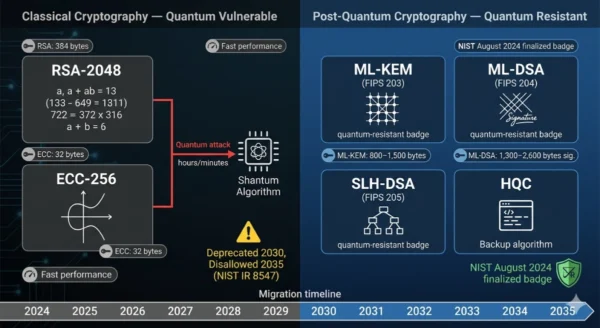
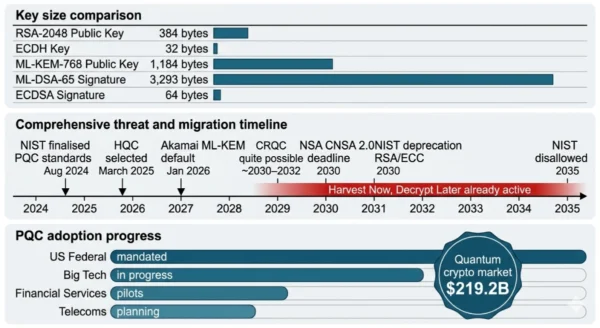
Post-Quantum Cryptography vs RSA/ECC is the cryptographic comparison that every security professional, developer, and IT leader must understand before 2030 — because that is the year NIST will officially deprecate RSA-2048 and ECC-256, and 2035 is when they will be completely disallowed in federal systems. The threat driving this timeline is Shor’s Algorithm: a quantum algorithm developed in 1994 that can efficiently solve the integer factorisation problem underlying RSA and the elliptic curve discrete logarithm problem underlying ECC — the two mathematical foundations that secure virtually every encrypted connection on the internet today. A sufficiently powerful quantum computer running Shor’s Algorithm could break RSA-2048 in hours or minutes rather than the billions of years a classical computer would require.
No such computer — a Cryptographically Relevant Quantum Computer, or CRQC — exists as of 2026. But the Global Risk Institute’s 2026 Quantum Threat Timeline estimates one is “quite possible” within ten years and “likely” within fifteen. More critically, the “harvest now, decrypt later” threat is already active: nation-state adversaries are collecting encrypted data today, storing it, and waiting for quantum capability to arrive.
In August 2024, NIST finalised three Post-Quantum Cryptography standards — FIPS 203 (ML-KEM), FIPS 204 (ML-DSA), and FIPS 205 (SLH-DSA) — ready to deploy now on existing infrastructure. In March 2025, HQC was selected as a fourth backup algorithm. Google has enabled ML-KEM in Chrome. Akamai made it default for all customers in January 2026. Microsoft has implemented PQC in Azure and Windows. The Post-Quantum Cryptography vs RSA/ECC migration is not a future planning exercise — it is an active security transition happening in 2026, and this comparison gives you everything you need to understand it.
Post-Quantum Cryptography vs RSA/ECC: The 2026 Cryptographic Landscape
The Post-Quantum Cryptography vs RSA/ECC transition is the most consequential infrastructure change in the history of internet security. Every protocol that protects digital communications — TLS/HTTPS, SSH, VPNs, JWT tokens, certificate chains, code signing, email encryption — relies on RSA or ECC at its core. These algorithms have been mathematically robust against classical computers for decades. They are not robust against quantum computers. NIST spent eight years — from 2016 to 2024 — running a global competition to find replacements.
In August 2024, it published the first three finalized Post-Quantum Cryptography standards.
The message from NIST is unambiguous: “There is no need to wait for future standards. Go ahead and start using these three.” In February 2026, Google issued a public call for governments and enterprises to “prepare now” for the quantum era of cybersecurity. In March 2026, Google’s Quantum AI team published a paper showing that future quantum computers could break Bitcoin’s core ECC in approximately nine minutes — using far fewer quantum resources than previously estimated.
Post-Quantum Cryptography vs RSA/ECC: Classical Cryptography Explained
What Are RSA and ECC?
RSA (Rivest–Shamir–Adleman) and ECC (Elliptic Curve Cryptography) are the two dominant public-key cryptographic systems securing virtually all digital communications today. RSA, introduced in 1977, derives its security from the computational difficulty of factoring the product of two large prime numbers — a problem that requires billions of years to solve using the best known classical algorithms at 2048-bit key sizes. ECC, introduced in the 1980s and standardised in the 1990s, derives its security from the elliptic curve discrete logarithm problem — computationally infeasible at 256-bit key sizes for classical computers.
Together, RSA and ECC underpin TLS/HTTPS (securing every web session), SSH (securing server access), VPNs (securing remote connections), digital certificates (verifying server identities), digital signatures (authenticating software, documents, and code), JWT and SAML tokens (securing authentication in apps), and email encryption (S/MIME, PGP). RSA-2048 and ECC-256 represent the current standard key sizes, balancing performance and security against classical attackers. Both are completely vulnerable to a quantum computer running Shor’s Algorithm, which solves their underlying mathematical problems in polynomial time — transforming a computation that takes billions of years into one that takes hours or minutes.
Strengths — Why RSA/ECC Have Dominated
- Decades of cryptanalysis: RSA has been the primary asymmetric algorithm since 1977 — nearly 50 years of intense academic and governmental scrutiny without a practical classical attack at 2048-bit key sizes
- Small key sizes: ECDH public keys are 32 bytes; ECDSA signatures are 64 bytes; RSA-2048 public keys are ~384 bytes — minimal bandwidth and storage overhead in protocols
- Fast performance: ECC operations are computationally efficient, enabling millions of TLS handshakes per second on modern server hardware with negligible latency impact
- Universal support: RSA and ECC are embedded in every operating system, browser, TLS library, HSM, smart card, and cryptographic module worldwide — the most widely deployed cryptographic infrastructure in history
- Well-understood failure modes: 50 years of research means security architects know precisely what attacks exist, what key sizes are secure, and how implementation errors manifest
- Hardware acceleration: Dedicated RSA and ECC accelerators exist in most enterprise-grade network devices, HSMs, and modern CPUs — implementation-optimised for latency and throughput
The Fatal Weakness: Quantum Vulnerability
- Shor’s Algorithm breaks both: Peter Shor’s 1994 quantum algorithm solves integer factorisation (RSA) and discrete logarithm (ECC/DH) in polynomial time — the mathematical problems that define both algorithms’ security are efficiently solvable on a quantum computer
- Breaking RSA-2048: Requires approximately 4,000 logical qubits running Shor’s Algorithm — could break RSA-2048 in hours or minutes on a sufficiently powerful quantum computer
- Breaking ECC-256: Recent research shows ~20x reduction in quantum resources required; ECC-256 could now be broken using fewer than ~500,000 physical qubits — faster than previously estimated
- HNDL threat is active today: Adversaries are collecting RSA/ECC-encrypted traffic now, before quantum computers exist — “harvest now, decrypt later” is not a future risk; it is a current data exposure
- NIST deprecation 2030: RSA-2048 and ECC-256 will be officially deprecated by 2030 and disallowed entirely by 2035 per NIST IR 8547 — a hard regulatory deadline
- No classical fix: Doubling RSA key sizes (to 4096-bit) does not solve the quantum threat — Shor’s Algorithm breaks RSA at any key size. Only a fundamentally different mathematical foundation provides quantum resistance
RSA and ECC Key Technical Parameters:
RSA: Security based on integer factorisation; typical key sizes 2048–4096 bits; public key ~384 bytes (2048-bit); used for key exchange (RSA-OAEP) and signatures (RSA-PSS, PKCS#1). ECC: Security based on elliptic curve discrete logarithm problem; typical key sizes 256–521 bits; ECDH public key 32 bytes; ECDSA signature 64 bytes; used in TLS, SSH, JWT, certificates. Furthermore, Quantum Attack: Shor’s Algorithm breaks both in polynomial time; ECC-256 breakable with ~500,000 physical qubits per recent research; RSA-2048 requires ~4,000 logical qubits. Additionally, NIST Timeline: Deprecated 2030; Disallowed 2035 (NIST IR 8547). Moreover, Current Deployment: Every TLS certificate, SSH key, VPN connection, code signing certificate, and JWT token in production uses RSA or ECC.
Post-Quantum Cryptography vs RSA/ECC: PQC Explained
What is Post-Quantum Cryptography?
Post-Quantum Cryptography (PQC), also called quantum-resistant or quantum-safe cryptography, refers to cryptographic algorithms designed to be secure against attacks by both classical and quantum computers. Unlike RSA and ECC, which derive their security from mathematical problems that Shor’s Algorithm can solve efficiently, PQC algorithms are based on mathematical problems for which no efficient quantum algorithm is currently known. NIST spent eight years evaluating 82 candidate algorithms submitted from cryptographers worldwide, narrowing them through four competitive rounds to the three algorithms finalised in August 2024.
A critical advantage of PQC over quantum key distribution (QKD): PQC algorithms run on existing classical hardware through software and firmware updates — no new specialised hardware is required. This makes PQC deployable immediately across the entire internet stack using standard CPUs, enabling a software migration rather than a hardware replacement programme. The three NIST PQC standards — ML-KEM (FIPS 203), ML-DSA (FIPS 204), and SLH-DSA (FIPS 205) — cover the two primary use cases of public-key cryptography: key establishment (how two parties agree on a shared encryption key) and digital signatures (how one party proves authenticity and integrity to another). In the Post-Quantum Cryptography vs RSA/ECC comparison, PQC introduces larger key and signature sizes as the primary trade-off for quantum resistance — a manageable engineering challenge that is being actively solved across the internet stack.
Strengths of Post-Quantum Cryptography
- Quantum resistance: Based on mathematical problems (lattice LWE, hash function hardness, code-based problems) for which no efficient quantum algorithm is known — resistant to Shor’s Algorithm by design
- Software-deployable: Runs on existing classical hardware — no quantum processors, specialised hardware, or fibre optic quantum channels required; migration is a software and configuration update
- NIST standardised: An eight-year international competition involving thousands of cryptographers vetted these algorithms — FIPS 203, 204, and 205 are the official US government standards, adopted by NATO and allied nations
- Algorithm diversity: NIST deliberately selected multiple mathematical foundations — lattices (ML-KEM, ML-DSA) for performance, hash functions (SLH-DSA) for conservative security, codes (HQC) as backup — providing resilience against unforeseen mathematical breakthroughs against any single approach
- Drop-in hybrid deployment: Hybrid modes (ML-KEM + X25519 for TLS) allow simultaneous deployment of PQC and classical algorithms, providing quantum safety while maintaining backward compatibility during the transition period
- ML-KEM performance competitive: ML-KEM offers faster key generation and encapsulation than RSA on modern hardware, with only modestly larger key sizes — “strong security and excellent performance” per NIST
Limitations and Migration Challenges
- Larger key and signature sizes: ML-KEM public keys are ~1,184 bytes vs ECDH’s 32 bytes; ML-DSA signatures are 2,400–4,600 bytes vs ECDSA’s 64 bytes — significant bandwidth and storage implications for certificate infrastructure, embedded systems, and constrained IoT devices
- Shorter track record: RSA/ECC have nearly 50 years of cryptanalysis; PQC algorithms have years, not decades, of peer review — lattice cryptography enjoys strong academic confidence, but algorithms are younger relative to RSA
- Implementation complexity: The mathematical foundations of lattice problems, hash trees, and coding theory are less familiar to most developers than RSA/ECC — correct, side-channel-resistant implementation requires specialist expertise
- Protocol migration scope: TLS, SSH, IPsec, certificates (X.509), code signing, JWT/SAML, OpenPGP, blockchain, PKI infrastructure — every protocol and system that uses RSA/ECC must be updated, touching virtually every layer of the IT stack
- IoT and constrained device challenge: Many deployed IoT sensors, smart meters, and embedded systems lack the compute power and memory for current PQC algorithms at reasonable performance — PQC on constrained devices requires careful algorithm selection (ML-KEM-512, Falcon-512)
- Certificate authority transition: The global PKI (public key infrastructure) — root CAs, intermediate CAs, TLS certificates, code signing certificates — all must transition to PQC, requiring coordination across thousands of organisations
Post-Quantum Cryptography Key Technical Parameters (NIST Standards 2024–2026):
ML-KEM (FIPS 203): Lattice-based key encapsulation; replaces RSA-OAEP and ECDH in key exchange; ML-KEM-768 public key 1,184 bytes, ciphertext 1,088 bytes; three parameter sets (512/768/1024) for different security levels. ML-DSA (FIPS 204): Lattice-based digital signatures; replaces ECDSA and RSA-PSS; signatures 2,400–4,600 bytes; public keys 1,300–2,600 bytes; three parameter sets (44/65/87). Furthermore, SLH-DSA (FIPS 205): Hash-based signatures; conservative security based on SHA-2/SHA-3 hardness; larger signatures (up to ~40KB in some variants); primary backup if lattice cryptography weaknesses emerge. HQC (selected March 2025): Code-based key encapsulation mechanism; backup to ML-KEM; standardisation ongoing; provides algorithm diversity independent of lattice assumptions. Additionally, Hybrid Deployment: X25519MLKEM768 is the de facto industry standard for PQC key exchange in browsers — combines classical ECDH with ML-KEM simultaneously for transition period safety.
Post-Quantum Cryptography vs RSA/ECC: The Quantum Threat Explained
Shor’s Algorithm: Why the Quantum Threat Is Existential
In 1994, mathematician Peter Shor proved that a quantum computer could efficiently solve two mathematical problems that underlie virtually all public-key cryptography: integer factorisation (RSA) and the discrete logarithm problem (ECC, Diffie-Hellman). “Efficiently” here means polynomial time — the computational resources required grow slowly as the problem size increases, rather than exponentially as they do for classical algorithms. This is not merely a performance improvement. It is a fundamental change in what is computationally possible. Classical computers require astronomical time (billions of years at 2048-bit RSA) to break these algorithms. A sufficiently powerful quantum computer running Shor’s Algorithm could break the same RSA-2048 key in hours or minutes.
How Shor’s Algorithm Breaks RSA
- RSA security depends on the difficulty of finding the prime factors p and q of a large number N = p × q (the public key)
- Classical computers require exponential time for this factorisation at 2048-bit sizes — billions of years with the best known algorithms
- Shor’s quantum algorithm uses quantum superposition and the quantum Fourier transform to find the period of a mathematical function related to N
- From this period, the prime factors can be derived in polynomial time — breaking RSA-2048 requires approximately 4,000 logical qubits
- With the private key exposed, all data encrypted with the corresponding RSA public key — past and present — can be decrypted
- Every TLS certificate, SSH key, code signing certificate, and encrypted email secured by RSA becomes trivially readable
How Shor’s Algorithm Breaks ECC
- ECC security depends on the elliptic curve discrete logarithm problem: given points P and Q = kP on an elliptic curve, finding k (the private key) is computationally infeasible classically
- Shor’s Algorithm also solves the discrete logarithm problem efficiently — applicable to both finite field and elliptic curve versions
- Recent research (2026) shows a ~20× reduction in quantum resources required to break ECC — ECC-256 could now be broken with fewer than ~500,000 physical qubits
- March 2026: Google’s Quantum AI team published a paper showing ECC (Bitcoin’s curve specifically) could be broken in approximately nine minutes on a future quantum computer
- All ECDH key exchanges (including TLS 1.3’s forward-secret sessions), ECDSA signatures, and Ed25519 keys are vulnerable
- ECC is used in virtually all modern TLS, SSH, JWT tokens, certificates, and cryptocurrency wallets — the scope of exposure is total
Harvest Now, Decrypt Later: The Threat That Is Active Today
Why You Need to Act Before Quantum Computers Exist
The most dangerous misconception about quantum cryptography is that the threat begins when quantum computers arrive. In reality, the threat begins when data is encrypted. Nation-state adversaries — intelligence agencies with the resources and motivation to act on long-term intelligence value — are operating HNDL programmes today: they intercept and store encrypted traffic at scale, preserving it indefinitely until the decryption capability arrives. Any data encrypted today that must remain confidential for five to ten or more years is already exposed. Medical records with 75-year retention requirements. Legal documents with multi-decade significance. Financial transaction records. Military communications. Government secrets. Long-lived signing keys. Software with multi-year certificate validity. The HNDL threat converts the Post-Quantum Cryptography vs RSA/ECC comparison from a future planning exercise into a present security obligation.
The Quantum Timeline: When Is the Risk Real?
| Source | CRQC Timeline Assessment | Implication |
|---|---|---|
| Global Risk Institute 2026 | “Quite possible” within 10 years; “likely” within 15 years | Data encrypted today may be at risk by 2031–2036 |
| Mainstream researchers | CRQC likely between 2030 and 2040 | Long-lived data (10+ year retention) should be protected now |
| US NSA | Planning PQC migration for National Security Systems by 2030 | Government threat assessment drives the 2030 operational deadline |
| Recent qubit research (2026) | ~20× reduction in resources to break ECC vs earlier estimates | Timeline may be compressing — conservative planning is prudent |
| IBM / Google quantum roadmaps | Error-corrected qubit milestones targeted 2028–2033 | CRQC-capable systems align with the 2030–2035 window |
Post-Quantum Cryptography vs RSA/ECC: NIST Standards Deep Dive
FIPS 203: ML-KEM
Full name: Module-Lattice-Based Key-Encapsulation Mechanism
Formerly: CRYSTALS-Kyber
Replaces: RSA-OAEP, ECDH, Diffie-Hellman in key exchange
Mathematical basis: Module Learning With Errors (MLWE) — given a matrix and approximate equation with hidden noise, recovering the secret is computationally hard classically and quantum-mechanically
Parameter sets:
- ML-KEM-512 (AES-128 equivalent) — fastest, smallest
- ML-KEM-768 (AES-192 equivalent) — recommended default
- ML-KEM-1024 (AES-256 equivalent) — maximum security
Key sizes (ML-KEM-768): Public key 1,184 bytes; ciphertext 1,088 bytes
Deployed by: Google Chrome (X25519MLKEM768 hybrid), Akamai (default Jan 2026), Microsoft Azure
FIPS 204: ML-DSA
Full name: Module-Lattice-Based Digital Signature Algorithm
Formerly: CRYSTALS-Dilithium
Replaces: ECDSA, RSA-PSS, EdDSA in digital signatures
Mathematical basis: Module Learning With Errors — same lattice family as ML-KEM, providing consistent security properties across both algorithms
Parameter sets:
- ML-DSA-44 (lower security) — faster, smaller signatures
- ML-DSA-65 (recommended) — balanced security and performance
- ML-DSA-87 (highest security) — for long-lived signatures
Key sizes (ML-DSA-65): Public key 1,952 bytes; signature 3,293 bytes
Use cases: TLS certificate signing, JWT tokens, SAML assertions, code signing, document integrity verification
FIPS 205: SLH-DSA
Full name: Stateless Hash-Based Digital Signature Algorithm
Formerly: SPHINCS+
Mathematical basis: Hash function hardness (SHA-2/SHA-3) — the most conservative possible PQC assumption; if SHA-256 remains secure, so does SLH-DSA
Role: Safety net and backup — if unforeseen mathematical advances weaken lattice-based ML-DSA, SLH-DSA (based on completely different mathematics) remains secure
Trade-offs: Larger signatures (tens of KB in some variants) and slower signing than ML-DSA, but extremely strong security foundations and no dependency on lattice assumptions
Best for: Firmware signing, long-lived documents, root certificate signing — use cases where maximum security conservatism outweighs performance
HQC and FN-DSA: Additional NIST Algorithms
HQC (Hamming Quasi-Cyclic) — Selected March 2025
NIST selected HQC in March 2025 as a backup key encapsulation mechanism to ML-KEM. HQC is based on error-correcting code decoding — a completely different mathematical assumption from ML-KEM’s lattice problems. Its selection is strategic: if unforeseen mathematical advances were to weaken lattice-based algorithms, HQC provides a code-based fallback for key encapsulation. Final standardisation is expected within 2026–2027. Organisations building new cryptographic systems should design for cryptographic agility — the ability to swap in HQC alongside or instead of ML-KEM without architectural changes.
FN-DSA (Falcon) — Ongoing Standardisation
FN-DSA (Falcon) is a lattice-based digital signature algorithm notable for its unusually small key and signature sizes compared to other PQC algorithms: an 897-byte public key and 666-byte signature for the 512-bit security variant — making it competitive with classical ECC signatures in size while remaining quantum-resistant. NIST is continuing standardisation of FN-DSA alongside the three primary FIPS standards. Its smaller size makes it particularly attractive for bandwidth-sensitive applications and constrained devices where ML-DSA’s 3+ KB signatures create significant overhead.
Hybrid Cryptography: The Bridge Strategy
During the transition period, the de facto industry approach is hybrid cryptography — running both a classical algorithm (for backward compatibility with systems that do not yet support PQC) and a post-quantum algorithm simultaneously, combining their outputs so that security holds as long as at least one remains unbroken. For TLS, the industry has standardised on X25519MLKEM768: combining the classical X25519 Elliptic Curve Diffie-Hellman with ML-KEM-768 in a single key exchange. This is already deployed in Chrome, Akamai (default from January 2026), Cloudflare, and other major TLS implementations. A session protected by X25519MLKEM768 is quantum-safe (because ML-KEM provides the post-quantum layer) and classically secure (because X25519 provides the classical layer) simultaneously.
12 Critical Differences: Post-Quantum Cryptography vs RSA/ECC
The Post-Quantum Cryptography vs RSA/ECC comparison below covers every key dimension — from mathematical foundations and quantum vulnerability to key sizes, performance, standardisation status, and migration requirements in 2026.
Aspect | RSA / ECC (Classical) | Post-Quantum Cryptography (PQC) |
|---|---|---|
| Mathematical Foundation | RSA: integer factorisation; ECC/DH: discrete logarithm problem — efficiently solvable by Shor’s Algorithm on a quantum computer | Lattice problems (LWE/MLWE), hash function hardness, error-correcting code decoding — no known efficient quantum algorithm for these problems |
| Quantum Resistance | None — Shor’s Algorithm breaks both RSA and ECC completely; ECC-256 breakable with ~500,000 physical qubits per recent research | Resistant to all known quantum attacks, including Shor’s Algorithm — specifically designed with quantum computer threat model as primary design requirement |
| Classical Security | Extremely well-studied — RSA has survived ~50 years of cryptanalysis; ECC ~40 years. Best known classical attacks require billions of years | Shorter track record — 8+ years of NIST competition review, strong academic confidence (especially lattice problems), but less historical depth than RSA/ECC |
| Key / Signature Sizes | RSA-2048 public key: ~384 bytes; ECDH key: 32 bytes; ECDSA signature: 64 bytes — minimal bandwidth overhead | ML-KEM-768 public key: 1,184 bytes; ML-DSA-65 signature: 3,293 bytes; 3–51x larger than classical equivalents depending on algorithm and use case |
| Performance (Speed) | ECC: very fast key generation and operations; RSA-2048: slower than ECC for key generation but fast for verification | ML-KEM: faster than RSA for key generation; comparable to ECC overall; ML-DSA: slower signing than ECDSA but acceptable for most applications |
| Standardisation Status | Decades-old standards — widely standardised in NIST, ISO, IETF, PKCS, TLS 1.3 and all major protocol suites. Actively being deprecated | FIPS 203/204/205 finalised August 2024; HQC selected March 2025; mandated for US federal systems; adoption progressing in TLS, SSH, PKI |
| NIST Regulatory Status | Deprecated by 2030 (NIST IR 8547); completely disallowed after 2035; Gartner: treat 2029 as operational deadline | The required replacement — NIST: “organisations should begin applying these standards now.” Mandatory for US federal systems, NSS by 2030 |
| Hardware / Infrastructure | Universal — every OS, browser, TLS library, HSM, certificate, smart card, and cryptographic module in production supports RSA/ECC | Software-deployable on existing hardware — growing hardware support in HSMs; IoT and constrained devices require careful algorithm selection (ML-KEM-512, Falcon-512) |
| HNDL Risk | Actively exposed — RSA/ECC-encrypted data intercepted today and stored by adversaries will be decryptable when a CRQC arrives | Immune — even when quantum computers arrive, data encrypted with PQC cannot be retrospectively decrypted using known quantum algorithms |
| Current Deployment | 100% of production TLS, SSH, VPN, PKI, JWT, code signing, and email encryption currently uses RSA or ECC — the entire internet runs on these algorithms | Google Chrome ML-KEM enabled; Akamai default Jan 2026; Microsoft Azure PQC; early-adopter enterprises in financial services, government, and defence |
| Migration Approach | N/A — the incumbent; all systems using RSA/ECC must be inventoried and migrated before regulatory deadlines | Hybrid first (X25519MLKEM768 for TLS), then pure PQC as ecosystem matures; cryptographic agility design enables future algorithm updates |
| Algorithm Diversity | Two mathematical families (factorisation + discrete log) — both broken by the same Shor’s Algorithm; no diversity against the quantum threat | Multiple independent mathematical families (lattices, hashes, codes) — if one is weakened, others provide backup; deliberate diversity by NIST design |
Post-Quantum Cryptography vs RSA/ECC: Migration Guide
Migration Complexity: Why This Requires a Programme, Not a Task
The Post-Quantum Cryptography vs RSA/ECC migration is not equivalent to updating a library dependency. RSA and ECC are embedded everywhere cryptography touches: TLS certificates and their entire PKI chain, SSH keys on every server, JWT signing keys in every authentication system, VPN configurations, code signing certificates with multi-year validity, encrypted backups, document signing workflows, hardware security modules, smart cards, IoT firmware signing, and third-party integrations. NIST’s own guidance states: “The transition to post-quantum cryptography involves more than just swapping algorithms — it’s a paradigm shift.” Microsoft has explicitly stated that Active Directory Certificate Services (AD CS) lacks a clear pathway to post-quantum solutions — highlighting that some infrastructure requires architectural rethinking rather than simple algorithm substitution. Gartner advises treating 2029 as the operational deadline rather than the formal 2030 NIST date, to allow for testing, certification, and supply chain dependencies.
Phase 1 — Discovery and Inventory (Immediate Priority)
Cryptographic Inventory
- Deploy automated cryptographic discovery tools — IBM Quantum Safe Explorer, open-source cbomkit, commercial alternatives from Cryptosense, Keyfactor, or Entrust — to scan all systems, code repositories, and dependencies for RSA/ECC usage
- Generate a Cryptographic Bill of Materials (CBOM) cataloguing every algorithm, key, certificate, and protocol in your environment — this is the foundational input for all subsequent migration planning
- Identify high-risk exposures: TLS certificates with multi-year validity, long-lived signing keys (code signing, document signing, root CAs), data with 10+ year retention requirements encrypted under RSA/ECC, and any systems processing data that must remain confidential for extended periods
- Classify your data by sensitivity and longevity — data that must remain confidential beyond 5–10 years is HNDL-exposed regardless of current quantum timeline estimates; prioritise this data for immediate protection
- Assess third-party dependencies — cloud providers, SaaS platforms, VPN vendors, HSM manufacturers, certificate authorities, and software supply chain partners all have their own PQC migration timelines that affect your readiness
Risk Prioritisation Framework
- Highest priority (migrate immediately): Any long-lived data encrypted under RSA/ECC that must remain confidential for 10+ years; root CA private keys; code signing keys used for software with extended deployment lifetimes; VPN and secure channel keys for systems storing highly sensitive data
- High priority (migrate by 2026–2027): TLS certificates and PKI infrastructure; JWT and SAML signing keys in authentication systems; SSH keys for privileged access; encrypted backup keys
- Medium priority (migrate by 2028–2029): Internal application encryption; database encryption at rest; email encryption infrastructure; document management systems
- Lower priority (migrate by 2030): Short-lived session data; ephemeral key exchange in modern TLS 1.3 (already forward-secret); data with short retention requirements
- IoT and embedded systems: assess separately — constrained devices may require firmware updates, hardware replacement, or algorithm selection optimised for resource constraints (ML-KEM-512, Falcon-512)
Phase 2 — Hybrid Deployment (2026–2027)
TLS Migration: Deploy Hybrid ML-KEM
- Enable X25519MLKEM768 hybrid key exchange in your TLS 1.3 configuration — this is the industry-standard hybrid combining classical X25519 with ML-KEM-768. Most modern TLS libraries (OpenSSL 3.x, BoringSSL, LibreSSL) support this in 2026
- Verify your web servers, load balancers, CDN (Akamai made this default in January 2026), and API gateways support the hybrid key exchange — prioritise internet-facing services first
- Test backward compatibility — hybrid modes are designed to fall back gracefully to classical algorithms for clients that do not support ML-KEM, maintaining compatibility during the transition period
- Plan for certificate migration — the IETF is standardising PQC certificate formats; first PQC certificates are expected in 2026, with broad browser trust likely by 2027. Monitor CA/Browser Forum ballots for ML-DSA certificate acceptance
- Monitor TLS performance impact — ML-KEM-768 adds approximately 1–2 KB to TLS handshakes; measure latency impact on your specific traffic patterns, particularly for mobile and high-latency connections
Code Signing and Authentication Migration
- Code signing (highest urgency per NSA): NSA guidance explicitly recommends adopting hash-based signatures (SLH-DSA / NIST SP 800-208 LMS/XMSS) for software and firmware signing immediately — signed software today will be verified years into the future when CRQCs may exist
- JWT / SAML authentication tokens: Monitor IETF working group progress on RFC standards for PQC JWT and SAML signing; prepare to update authentication libraries to ML-DSA signing as RFCs are finalised
- SSH keys: Generate new SSH keypairs using ML-DSA or SLH-DSA in addition to existing Ed25519 keys — maintain both during transition; SSH protocol PQC extensions are standardised in IETF drafts
- VPN configurations: IPsec PQC extensions are in active IETF standardisation; update VPN products to support ML-KEM for key exchange in IKEv2 — most enterprise VPN vendors have published PQC roadmaps for 2026–2027
- HSM compatibility: Confirm hardware security module vendors (Thales, Utimaco, Entrust, AWS CloudHSM) support NIST PQC algorithms — SEALSQ and other HSM vendors target 2025–2026 for NIST-approved PQC integration
Phase 3 — Full Migration and Cryptographic Agility (2027–2030)
- Design for cryptographic agility from today: Any new system built in 2026 and beyond should treat the cryptographic algorithm as a configurable parameter rather than a hard-coded constant — enabling future algorithm transitions without architectural changes. This is the single highest-ROI investment in long-term security posture
- Root CA transition: The migration of root and intermediate certificate authorities to PQC algorithms is the most complex PKI challenge — requiring industry-wide coordination through CA/Browser Forum and careful management of certificate chain trust. Monitor CA/B Forum ballots and certificate transparency logs for PQC certificate issuance timelines
- Retire RSA/ECC assets on schedule: As PQC-equivalent assets are deployed, actively retire the corresponding RSA/ECC keys, certificates, and configurations — do not leave both active in parallel indefinitely, as this creates maintenance complexity and potential confusion about which is the authoritative key material
- Supply chain compliance: US and Canadian government mandates create cascading compliance requirements through procurement chains — any organisation supplying technology to government agencies will face PQC compliance requirements as a condition of contract, extending the migration mandate into the private sector
- Monitor NIST’s ongoing standardisation: FN-DSA (Falcon) standardisation is ongoing; the Signatures Onramp competition may produce additional PQC signature algorithms before 2030; HQC standardisation is progressing. Cryptographic agility positions you to adopt improvements as the ecosystem matures without architectural rework
Post-Quantum Cryptography vs RSA/ECC: Key Sizes, Performance and Market Data
NIST Deprecation
2030
RSA-2048 and ECC-256 officially deprecated; disallowed entirely 2035 per NIST IR 8547
CRQC Timeline
~10–15 yr
Global Risk Institute 2026: CRQC “quite possible” within 10 years; “likely” within 15
Market Size
$219.2B
Global quantum cryptography market value (IDC) driving PQC investment
ECC Qubit Reduction
~20×
Reduction in quantum resources required to break ECC vs earlier estimates — timeline compressing
Key Size Comparison: Post-Quantum Cryptography vs RSA/ECC
| Algorithm | Type | Public Key Size | Ciphertext / Signature Size | vs Classical Equivalent |
|---|---|---|---|---|
| RSA-2048 | Classical (key exchange + signature) | ~384 bytes | 256 bytes (ciphertext) / 256 bytes (signature) | Baseline for comparison |
| ECDH P-256 | Classical (key exchange) | 32 bytes | 32 bytes (shared secret) | Baseline for comparison |
| ECDSA P-256 | Classical (digital signature) | 64 bytes | 64–72 bytes (signature) | Baseline for comparison |
| ML-KEM-512 (FIPS 203) | PQC key encapsulation | 800 bytes | 768 bytes (ciphertext) | ~25× larger than ECDH |
| ML-KEM-768 (FIPS 203) ★ | PQC key encapsulation (recommended) | 1,184 bytes | 1,088 bytes (ciphertext) | ~37× larger than ECDH |
| ML-DSA-65 (FIPS 204) ★ | PQC digital signature (recommended) | 1,952 bytes | 3,293 bytes (signature) | ~51× larger than ECDSA |
| SLH-DSA (FIPS 205) | PQC hash-based signature | 32–64 bytes | 7,856–49,856 bytes (signature) | Conservative, larger variants |
| FN-DSA / Falcon-512 (ongoing) | PQC digital signature (compact) | 897 bytes | 666 bytes (signature) | ~10× ECDSA — smallest PQC sig |
Industry Adoption Progress: Post-Quantum Cryptography vs RSA/ECC in 2026
| Organisation / Sector | PQC Status | Key Actions |
|---|---|---|
| Deployed | ML-KEM enabled in Chrome (X25519MLKEM768 hybrid); Quantum AI research accelerating timeline awareness | |
| Akamai | Default (Jan 2026) | ML-KEM default for all customer TLS from January 31, 2026; PQC to origins opt-in available |
| Microsoft | Implemented | PQC in Azure services and Windows updates; Azure Key Vault PQC support rolling out |
| AWS | In progress | AWS KMS PQC roadmap; ACM certificate manager PQC planning; TLS PQC across CloudFront |
| US Federal Government | Mandated | OMB directed agencies to begin PQC migration planning; NSA CNSA 2.0 requires NSS migration by 2030 |
| Canada | Mandated timelines | PQC migration plans required by April 2026; priority systems by 2031; full migration by 2035 |
| Financial Services | Pilot phase | Large banks and payment networks beginning PQC pilots; high-value data sensitivity driving urgency |
| Telecommunications | Standards phase | 5G and 6G standards incorporating PQC; widespread implementation awaits device ecosystem maturation |
Post-Quantum Cryptography vs RSA/ECC: Decision Framework
The Core Question: When Is Your Data at Risk?
The Post-Quantum Cryptography vs RSA/ECC decision is not a question of “if” but “when.” RSA and ECC will be replaced — NIST’s deadline is final. The decision is how urgently your specific organisation needs to act, which is determined by the sensitivity and longevity of your data. A company that encrypts session tokens with 24-hour expiry has a completely different risk profile from a hospital encrypting patient records with 75-year retention requirements, or a government agency encrypting classified communications that must remain secret for decades.
Act Immediately (High HNDL Risk):
- You handle data that must remain confidential for 10+ years — medical records, legal documents, government secrets, financial records with long retention requirements
- You are in a regulated sector under NIST/NSA mandate — US federal contractor, defence supply chain, national security systems (NSS) — the 2030 deadline is a hard compliance requirement
- Your signing keys have multi-year validity — code signing certificates, root CAs, document signing keys that will be used to verify content long into the future
- You operate critical infrastructure — power grids, financial systems, telecommunications — where the asymmetric information threat from a CRQC has strategic national security implications
- You are in healthcare, where HIPAA mandates data protection for decades and medical records represent long-lived sensitive data directly exposed to HNDL attacks
- Your organisation operates in multiple jurisdictions with overlapping PQC mandates — Canada’s April 2026 plan deadline, EU regulatory frameworks, NIST requirements
Begin Planning Now (Standard Timeline):
- You are a commercial enterprise without specific regulatory mandates but you manage customer data, payment information, or proprietary intellectual property — the NIST 2030 deprecation affects your entire cryptographic stack
- You are a software developer building systems today — any application you design now should be built with cryptographic agility and PQC readiness as architectural requirements
- You manage TLS certificates, PKI infrastructure, or authentication systems — the certificate migration timeline is long enough that planning must begin in 2026 to meet 2029–2030 operational deadlines
- Your technology stack includes vendor-managed cryptography — cloud services, SaaS platforms, enterprise software — requiring coordination with vendor PQC roadmaps that you should be tracking now
- You are in financial services, where even without current mandates, the value of financial data and regulatory attention make early migration strategically prudent
- You ship software — code signing with SLH-DSA should begin immediately per NSA guidance, as signed software must be verified long after quantum computers exist
PQC vs RSA/ECC Quick Decision Table
| Situation | Recommended Action | Priority |
|---|---|---|
| Building a new web service in 2026 | Design for X25519MLKEM768 TLS + ML-DSA JWT signing from day one | Immediate |
| Medical record system with 75-year retention | Begin PQC migration now — HNDL threat is already active for this data | Critical |
| US federal contractor | NIST compliance required — begin inventory now; NSS requires PQC by 2030 | Mandatory |
| E-commerce TLS certificates | Deploy hybrid ML-KEM TLS; plan for ML-DSA certificates in 2027 | High |
| Internal employee tools, short session data | Include in migration programme but lower priority than long-lived data | Medium |
| IoT/embedded device firmware | Evaluate SLH-DSA for OTA signing now; plan hardware refresh for device PQC | High (signing) |
| Legacy system with no PQC roadmap | Prioritise for replacement or isolation; document as technical debt | High |
| VPN infrastructure | Update to ML-KEM-based IKEv2 key exchange as vendors release PQC updates | High |
| Code signing certificates | Migrate to SLH-DSA or LMS/XMSS immediately per NSA guidance | Critical |
| Cryptocurrency/blockchain | Evaluate PQC migration paths — blockchain wallets using ECC-256 are CRQC-vulnerable | High |
Frequently Asked Questions
The fundamental difference between Post-Quantum Cryptography vs RSA/ECC is the mathematical problem each uses for security and whether that problem is solvable by a quantum computer. RSA derives security from the difficulty of factoring large numbers; ECC derives security from the elliptic curve discrete logarithm problem. Both are efficiently solvable by Shor’s Algorithm on a quantum computer — making RSA and ECC completely insecure against quantum attacks.
Post-Quantum Cryptography uses entirely different mathematical foundations: lattice problems (the Learning With Errors problem underlying ML-KEM and ML-DSA), hash function hardness (SLH-DSA), and error-correcting code decoding (HQC). No efficient quantum algorithm is currently known for any of these problem classes. The practical consequence: RSA and ECC will be deprecated by 2030 and disallowed by 2035 per NIST IR 8547. ML-KEM, ML-DSA, and SLH-DSA are the standardised replacements, ready to deploy now on existing hardware.
No Cryptographically Relevant Quantum Computer (CRQC) exists as of 2026 — current quantum computers are too small and error-prone to run Shor’s Algorithm on real cryptographic key sizes. The timeline is genuinely uncertain, but the expert consensus has narrowed. The Global Risk Institute’s 2026 Quantum Threat Timeline estimates a CRQC is “quite possible” within ten years and “likely” within fifteen. Mainstream researchers estimate a CRQC likely between 2030 and 2040.
Breaking RSA-2048 requires approximately 4,000 logical qubits (millions of physical qubits accounting for error correction). Breaking ECC-256 now appears achievable with fewer than ~500,000 physical qubits following recent research showing a ~20× reduction in required resources. Google’s Quantum AI team published a March 2026 paper showing ECC could be broken in approximately nine minutes on a sufficiently advanced future quantum computer. The uncertainty in the exact date is precisely why the “harvest now, decrypt later” threat is so important: adversaries who collect encrypted data today need only wait for the quantum capability to arrive, which means data with 10+ year confidentiality requirements is already exposed.
Harvest Now, Decrypt Later (HNDL), also called “store now, decrypt later” or the “retrospective decryption threat,” is a data collection strategy where adversaries — typically nation-state intelligence agencies — intercept and archive encrypted network traffic today, store it at scale, and plan to decrypt it retrospectively once quantum computing capability becomes available. The threat is active because encrypted data from a TLS session, a VPN tunnel, or an encrypted file is mathematically identical whether collected today or in five years — the mathematical operations required to decrypt it are the same.
An adversary who stores an encrypted RSA session today needs only wait for a CRQC to arrive to read its contents. This is why the PQC vs RSA/ECC migration is urgent even though no CRQC exists in 2026. Any data that must remain confidential for longer than the expected quantum timeline (~10–15 years) — medical records, legal communications, government secrets, long-lived financial records, software signing keys — is already exposed to retrospective decryption by any adversary collecting and archiving encrypted traffic today. This converts what seems like a future problem into a present security obligation.
NIST finalised three Post-Quantum Cryptography standards in August 2024 after an eight-year international competition. FIPS 203 (ML-KEM, formerly CRYSTALS-Kyber) is a key encapsulation mechanism that replaces RSA key exchange (RSA-OAEP), Diffie-Hellman (DH), and Elliptic Curve Diffie-Hellman (ECDH) in protocols like TLS. ML-KEM-768 is the recommended default, with a 1,184-byte public key and 1,088-byte ciphertext versus ECDH’s 32-byte key — larger, but fast enough for real-time use. FIPS 204 (ML-DSA, formerly CRYSTALS-Dilithium) is a digital signature algorithm that replaces ECDSA, RSA-PSS, and EdDSA in certificate signing, JWT tokens, SAML assertions, code signing, and document integrity. ML-DSA-65 is the recommended default with 3,293-byte signatures versus ECDSA’s 64 bytes.
FIPS 205 (SLH-DSA, formerly SPHINCS+) is a hash-based digital signature scheme based on SHA-2/SHA-3 hardness, serving as a conservative backup to ML-DSA. In March 2025, NIST selected HQC as a fourth code-based backup key encapsulation mechanism. FN-DSA (Falcon) standardisation is also ongoing, offering notably smaller signatures than ML-DSA. NIST’s explicit guidance: “There is no need to wait for future standards. Go ahead and start using these three.”
Post-Quantum Cryptography algorithms have significantly larger key and signature sizes than their RSA and ECC equivalents — this is the primary engineering trade-off. For key exchange: ECDH uses 32-byte public keys, while ML-KEM-768 uses 1,184-byte public keys (approximately 37× larger) with 1,088-byte ciphertexts. For digital signatures: ECDSA produces 64-byte signatures, while ML-DSA-65 produces 3,293-byte signatures (approximately 51× larger) with 1,952-byte public keys.
For comparison with RSA: RSA-2048 public keys are approximately 384 bytes — ML-KEM-768 is roughly 3× larger. The exception is FN-DSA (Falcon), which produces 666-byte signatures — approximately 10× ECDSA but far smaller than ML-DSA. SLH-DSA signatures can range from 7,856 to 49,856 bytes depending on parameter variant, reflecting its conservative mathematical approach. In practice, the additional bandwidth overhead is manageable for most applications — TLS handshakes increase by 1–2 KB with hybrid ML-KEM, and most modern network infrastructure handles this without meaningful latency impact. The most challenging environments are bandwidth-constrained IoT devices, smart cards, and embedded systems where smaller algorithms like ML-KEM-512 and Falcon-512 are preferred.
No — doubling RSA key size does not solve the quantum threat and is not a viable mitigation strategy. Shor’s Algorithm breaks RSA at any key size in polynomial time — the computational resources required grow only polynomially with key size rather than exponentially. Moving from RSA-2048 to RSA-4096 slightly increases the number of quantum operations required but does not change the fundamental attack feasibility. A CRQC that can break RSA-2048 in hours can break RSA-4096 in somewhat more time — still within practical reach for a motivated adversary with quantum capability. Increasing key sizes does provide additional security against classical attacks — RSA-4096 offers significantly more classical security margin than RSA-2048 — but provides no meaningful protection against quantum attacks.
This is distinct from symmetric cryptography (AES, SHA): Grover’s quantum algorithm provides only a quadratic speedup against AES key search, meaning AES-256 remains quantum-secure (a quantum computer gains only the equivalent of halving the key size, effectively reducing AES-256 to AES-128 security against quantum attacks). For symmetric cryptography, doubling key sizes is sufficient. For RSA and ECC, only a fundamentally different mathematical foundation — which is exactly what PQC provides — offers quantum resistance.
Hybrid cryptography runs a classical algorithm (e.g., X25519 ECDH) and a post-quantum algorithm (e.g., ML-KEM-768) simultaneously in the same cryptographic operation, combining their outputs into a single shared secret or key. The security property of a properly implemented hybrid is that breaking it requires breaking both algorithms — so a session protected by X25519MLKEM768 is secure as long as either ECDH or ML-KEM remains unbroken. This approach is recommended as the migration strategy for two reasons.
First, backward compatibility: hybrid modes can fall back gracefully to classical algorithms for endpoints that do not yet support ML-KEM, maintaining interoperability during the multi-year transition period when both PQC and non-PQC systems are in production simultaneously. Second, insurance against PQC uncertainty: PQC algorithms are newer with a shorter cryptanalytic track record than RSA/ECC. A hybrid approach provides quantum safety from ML-KEM while classical security from ECDH provides a safety net if unforeseen weaknesses in the PQC algorithm emerge. X25519MLKEM768 is the de facto industry standard for TLS PQC key exchange — deployed by Google Chrome, Akamai (default from January 2026), Cloudflare, and most major TLS implementations.
Symmetric encryption algorithms like AES and hash functions like SHA-256 are significantly less vulnerable to quantum attacks than RSA and ECC, and the mitigation is straightforward. The relevant quantum algorithm for symmetric cryptography is Grover’s Algorithm, which provides a quadratic speedup for searching an unstructured database — applied to AES, this effectively halves the key length in terms of security. AES-128 (with 128-bit key) would be reduced to approximately 64-bit classical equivalent security by a quantum computer, which is considered potentially inadequate for long-term security.
AES-256 would be reduced to approximately 128-bit classical equivalent — still secure for any foreseeable threat. For SHA-256 and SHA-3, Grover’s Algorithm affects preimage resistance; collision resistance requires more complex analysis. NIST’s current assessment is that SHA-256 remains secure for hash functions, and AES-256 remains secure for encryption. The practical guidance: if you are using AES-128, consider upgrading to AES-256 for long-lived data. If you are using AES-256, no change is required for quantum resistance. SHA-256 remains acceptable; SHA-384 or SHA-512 provide additional security margin. The critical distinction from RSA/ECC: symmetric algorithms require parameter adjustment, not complete replacement.
Cryptographic agility is the architectural property of a system that allows its cryptographic algorithms to be updated, swapped, or reconfigured without requiring changes to the broader system architecture. A cryptographically agile system treats the algorithm as a parameter rather than a hard-coded implementation detail — enabling the system to adopt ML-KEM today, switch to HQC if a lattice vulnerability is discovered, or adopt a future algorithm that emerges from NIST’s ongoing standardisation rounds, all without architectural redesign. Cryptographic agility is the most important architectural principle for 2026 for three reasons.
First, the PQC field is still maturing: NIST’s Signatures Onramp competition is evaluating additional algorithms; FN-DSA and HQC are in final standardisation; new competition winners will emerge before 2030. A cryptographically agile system can adopt improvements as they arrive. Second, NIST’s FIPS 203/204/205 are not the last word: SIKE was broken during the competition; future cryptanalysis may weaken assumptions in currently standardised algorithms. The ability to switch algorithms rapidly is as important as choosing the right algorithm initially. Third, the RSA/ECC deprecation creates a single migration deadline: systems that are cryptographically agile can meet that deadline by updating configuration; systems with hard-coded RSA/ECC require architectural rework. For any system designed or rebuilt in 2026, cryptographic agility is a fundamental design requirement, not a bonus feature.
Blockchain and cryptocurrency systems face a serious quantum threat because their security foundations are entirely based on the elliptic curve cryptography that quantum computers can break. Bitcoin wallets use ECDSA with the secp256k1 curve — the same mathematical problem Shor’s Algorithm solves — to generate public/private key pairs and sign transactions. A CRQC with sufficient qubits could derive a wallet’s private key from its public key, enabling the theft of any funds in that wallet. In March 2026, Google’s Quantum AI team published a paper showing Bitcoin’s specific ECC implementation could be broken in approximately nine minutes on a sufficiently advanced quantum computer.
Public blockchain addresses whose public keys have been exposed (i.e., the wallet has previously made a transaction) are directly vulnerable — the public key is visible on-chain and derivable by a quantum attacker. Addresses whose public keys have never been broadcast (spent zero transactions) are less immediately vulnerable. The blockchain community is aware of this threat and PQC migration efforts are underway, but the challenge is immense: migrating a decentralised protocol where participants cannot be forced to update requires achieving broad community consensus, and the migration path involves moving funds from quantum-vulnerable addresses to new PQC-secured addresses before a CRQC arrives. Several blockchain projects are exploring PQC-native chains and protocol upgrades. As of 2026, no major public blockchain has completed a quantum-resistant migration, creating a significant systemic risk that grows as the CRQC timeline compresses.
Post-Quantum Cryptography vs RSA/ECC: Final Takeaways for 2026
The Post-Quantum Cryptography vs RSA/ECC comparison reaches an unambiguous conclusion: RSA and ECC are being replaced, the timeline is set, the standards are published, and the migration is underway. The only question is whether your organisation is positioned to complete this transition before the regulatory deadlines — and before the data you encrypted under RSA/ECC today becomes retrospectively readable.
RSA/ECC — Key Takeaways:
- Secure against classical computers — insecure against quantum
- Shor’s Algorithm breaks both: RSA (factorisation) and ECC (discrete log)
- ECC-256 breakable with ~500,000 physical qubits (recent research)
- HNDL attacks active today — stored data vulnerable when CRQC arrives
- NIST: deprecated 2030, disallowed 2035 (NIST IR 8547)
- Small keys (32–384 bytes), fast, universal support — but a dead end
Post-Quantum Cryptography — Key Takeaways:
- Three NIST standards finalised August 2024: ML-KEM, ML-DSA, SLH-DSA
- HQC selected March 2025 — code-based backup for ML-KEM
- Software-deployable on existing hardware — no new hardware required
- Larger keys (800–4,600 bytes) — manageable for most applications
- Google Chrome ML-KEM deployed; Akamai default Jan 2026; Microsoft Azure
- Gartner: treat 2029 as the operational deadline for migration
Practical Recommendations for 2026:
If you are a developer: Design every new system with cryptographic agility. Enable X25519MLKEM768 hybrid TLS on all internet-facing services today — this is a configuration change in most modern TLS deployments and requires no architectural changes. Build PQC key exchange and signature support into your authentication systems now.
If you are a CISO or security architect: Begin your cryptographic inventory immediately using automated tools. Classify your data by retention period and sensitivity to identify HNDL-exposed assets. Prioritise code signing migration to SLH-DSA per NSA guidance. Develop a migration programme with internal deadlines tracking ahead of NIST’s 2030 date.
If you operate regulated systems: The NIST IR 8547 timeline is a hard regulatory deadline. NSA CNSA 2.0 requires National Security Systems to complete PQC migration by 2030. Canada requires migration plans by April 2026. These are not advisories — they are requirements with supply chain implications.
The one non-negotiable: The Post-Quantum Cryptography vs RSA/ECC migration will happen. The only question is whether your organisation plans and executes it on your own timeline, or scrambles to comply under regulatory pressure when deadlines arrive. 2026 is the planning and early implementation year. 2029 is the operational deadline. 2035 is the hard cutoff.
Related Topics Worth Exploring
Zero Trust vs Perimeter Security
Post-Quantum Cryptography secures the mathematical layer of authentication and encryption. Zero Trust architecture secures the access control layer — verifying every user, device, and connection regardless of network location. Together they represent the complete security modernisation framework that CISOs are implementing in 2026 to address both quantum and non-quantum threats.
DevSecOps vs DevOps
The PQC migration requires embedding cryptographic compliance into every software pipeline — detecting RSA/ECC dependencies in code, enforcing PQC-ready algorithm policies in CI/CD, and automating certificate rotation. DevSecOps provides the delivery model for making cryptographic agility a continuous practice rather than a one-time migration event.
Quantum Computing vs Classical Computing
Post-Quantum Cryptography vs RSA/ECC is the cryptographic response to the quantum computing threat. Understanding why quantum computers are fundamentally different from classical computers — how qubits and superposition enable Shor’s Algorithm — provides the essential foundation for understanding why the migration is mathematically necessary, not merely regulatory.