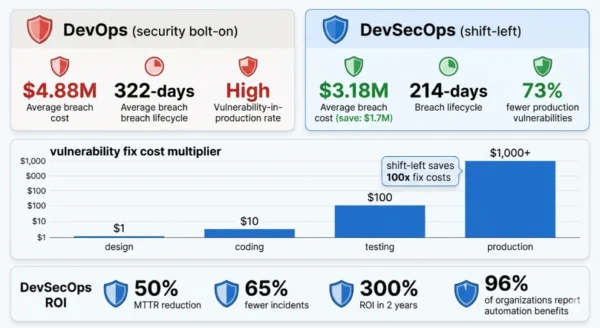
DevSecOps vs DevOps is the most consequential architectural choice in software delivery for 2026 — and most organizations are still getting it wrong. The average data breach now costs $4.88 million, up 10% in a single year, yet 81% of engineering teams admit to knowingly shipping vulnerable code under deadline pressure. Traditional DevOps solved the collaboration problem between development and operations and transformed how fast software ships. DevSecOps solves the next problem: making that speed sustainable without trading security for velocity. The difference between DevSecOps vs DevOps is not a tooling choice — it is a philosophical shift from treating security as a gate at the end of the pipeline to embedding it as an automated, continuous responsibility at every stage.
Organizations with high DevSecOps adoption save nearly $1.7 million per data breach compared to those without, according to IBM’s 2024 Cost of a Data Breach report. Add AI and automation, and the savings reach an additional $2.2 million per incident. The DevSecOps market reached $10 billion in 2026 and is projected to grow to $37 billion by 2035 — driven by regulatory pressure, cloud-native complexity, AI-generated code risk, and the brutal economics of fixing vulnerabilities in production versus catching them at design. Whether you are a student learning modern development practices, a developer writing your first secure pipeline, or a CISO evaluating your organization’s security posture — this DevSecOps vs DevOps comparison gives you every dimension you need to understand the shift, justify the investment, and implement the change.
DevSecOps vs DevOps: The Security-Speed Landscape in 2026
DevSecOps vs DevOps represents the central tension in modern software engineering: how do you ship faster without making your systems less safe? DevOps answered the first half of that question brilliantly — breaking down silos between developers and operations, automating delivery pipelines, and enabling organizations to deploy code orders of magnitude more frequently than before. But speed without security is not progress. The same CI/CD pipelines that accelerate delivery also accelerate the path from a vulnerable dependency to a production breach if security is treated as an afterthought.
DevSecOps vs DevOps: The DevOps Foundation
Definition
DevOps is a culture, methodology, and set of practices that integrates software development (Dev) and IT operations (Ops) into a continuous, collaborative delivery process. Originating from the Agile movement and formally named at the Agile Conference in 2008, DevOps breaks down the traditional silos between developers who write code and operators who run systems — replacing handoffs and blame cycles with shared ownership, automated pipelines, and continuous feedback. The core pillars of DevOps are Continuous Integration (CI), Continuous Delivery and Deployment (CD), infrastructure as code, automated testing, monitoring, and a culture of collaboration and shared accountability. DevOps is not a tool or a job title — it is a philosophy operationalized through practices and toolchains. Today, 80% of organizations practice some form of DevOps, and the global DevOps market is projected to reach $25.5 billion by 2028. Elite DevOps teams deploy code 208 times more frequently and recover from incidents 2,604 times faster than low-performing organizations. DevOps transformed software delivery — but in the DevSecOps vs DevOps comparison, its critical gap is that security was never architecturally integrated into its foundation.
Strengths and Advantages
- Deployment velocity: Elite DevOps teams deploy on-demand multiple times per day — continuous integration and automated testing compress release cycles from months to hours
- Developer experience: Shared ownership, fast feedback loops, and automated pipelines reduce cognitive load and prevent the burnout caused by manual, siloed release processes
- Reliability and recovery: Continuous monitoring, automated rollbacks, and shared operational responsibility dramatically reduce mean time to recovery (MTTR) from incidents
- Infrastructure as code: IaC tools like Terraform and Pulumi make infrastructure reproducible, version-controlled, and auditable — a core DevOps practice that DevSecOps extends with security scanning
- Mature ecosystem: 15+ years of tooling, best practices, certifications, and community knowledge — Jenkins, GitHub Actions, Docker, Kubernetes, and Terraform all have deep DevOps roots
- Cultural foundation: The collaboration and automation mindset DevOps establishes is the prerequisite for a successful DevSecOps transition — you cannot shift security left without the pipeline to shift it into
Security Gaps and Limitations
- Security as an afterthought: Traditional DevOps pipelines treat security as a pre-release gate — a manual review that slows deployment and is routinely skipped under deadline pressure
- Vulnerability-in-production risk: Without automated scanning at every pipeline stage, vulnerable dependencies, misconfigurations, and insecure code reach production before detection
- Developer-security disconnect: DevOps creates Dev-Ops collaboration but leaves the Security team as a separate, external function — the “security team throws vulnerabilities over the wall” problem persists
- Open-source blind spot: 97% of commercial codebases contain open-source components; without SCA scanning in the pipeline, known CVEs enter production through dependencies
- AI code risk: 97% of organizations use or plan to use AI in the SDLC — AI-generated code introduces new vulnerability patterns that manual review processes cannot scale to address
- Compliance friction: Regulated industries increasingly require demonstrable security controls at every pipeline stage — traditional DevOps cannot produce the automated audit evidence that GDPR, SOC 2, and PCI DSS demand
DevOps Core Technical Parameters:
CI/CD Pipeline: Continuous Integration (automated build and test on every commit) plus Continuous Delivery/Deployment (automated release to staging and production). IaC: Infrastructure defined as code using Terraform, Pulumi, Ansible, or CloudFormation — version-controlled and repeatable. Monitoring: Observability stack (metrics, logs, traces) providing real-time visibility into system health and deployment impact. Furthermore, Collaboration Model: Shared ownership between Dev and Ops — on-call rotations, blameless post-mortems, and cross-functional teams. Additionally, Automation Coverage: Build, test, deploy, and rollback automated — manual intervention minimized across the delivery pipeline. Moreover, Feedback Loops: Rapid feedback from automated tests, deployment metrics, and production monitoring accelerates iteration cycles.
DevSecOps vs DevOps: What DevSecOps Adds
Definition
DevSecOps extends DevOps by making security a shared, continuous, and automated responsibility throughout the entire software development lifecycle — not a separate team’s problem or a final-stage gate. The “shift-left” principle at its core means moving security activities earlier in the pipeline: threat modeling during planning, static application security testing (SAST) at code commit, software composition analysis (SCA) during builds, dynamic application security testing (DAST) in test environments, infrastructure-as-code security scanning before deployment, and runtime application self-protection (RASP) plus continuous security monitoring in production. In the DevSecOps vs DevOps framework, the key distinction is that security is no longer a handoff — it is embedded as automated checks, policy gates, and developer feedback at every stage. DevSecOps does not slow development down — when implemented with automation, it catches vulnerabilities when they are cheapest to fix (at design: $1; in production: $1,000+) and eliminates the costly rework cycles of late-stage security reviews. The DevSecOps market reached $10 billion in 2026, driven by organizations realizing that the cost of NOT embedding security — measured in breach costs, regulatory fines, and remediation labor — exceeds the cost of building it in.
Strengths and Advantages
- Shift-left cost reduction: Fixing a vulnerability at design costs $1; at production it costs $1,000+. Automated scanning catches issues when remediation is 100–1,000x cheaper than production discovery
- Breach cost reduction: IBM 2024 data shows high DevSecOps adoption saves $1.7 million per breach; adding AI and automation saves an additional $2.2 million — a potential $3.9 million total reduction per incident
- Faster vulnerability remediation: DevSecOps reduces mean time to remediate (MTTR) vulnerabilities by 50% — automated detection and developer-proximate feedback eliminates the ticket queue between security teams and engineers
- Compliance automation: Automated policy gates produce continuous audit evidence for GDPR, SOC 2, PCI DSS, HIPAA, and FedRAMP — dramatically reducing compliance overhead compared to manual DevOps review processes
- Supply chain security: SCA scanning identifies vulnerable open-source dependencies before they reach production — critical when 81% of codebases contain at least one high or critical open-source vulnerability
- AI code governance: DevSecOps pipelines can gate AI-generated code through the same SAST and SCA controls as human-written code — essential as AI writes an increasing share of production code in 2026
Challenges and Limitations
- Skills shortage: 45% of organizations cite lack of DevSecOps skills as the top implementation barrier — engineers who combine security knowledge with DevOps platform expertise are rare and expensive
- Cultural resistance: 51% report cultural resistance as a major barrier — developers see security scanning as friction, and security teams resist losing control of their review gate
- CI/CD integration complexity: 62% of organizations struggle to integrate security tools into existing CI/CD pipelines — tooling sprawl, false positive tuning, and pipeline performance impact create real friction
- False positive fatigue: Immature SAST and DAST configurations generate excessive false positives that developers learn to ignore — reducing the effectiveness of security gates without proper tuning
- Tool sprawl: A full DevSecOps toolchain spans SAST, DAST, SCA, IaC scanning, secrets detection, container scanning, CSPM, and more — managing, licensing, and integrating all these tools creates real overhead
- Performance overhead: Comprehensive security scanning adds pipeline execution time — organizations must balance scan depth with developer feedback speed to avoid security becoming a bottleneck
DevSecOps Core Technical Parameters:
SAST (Static Application Security Testing): Scans source code for known vulnerability patterns at commit or build time — tools include Semgrep, SonarQube, Checkmarx, Veracode. DAST (Dynamic Application Security Testing): Tests running applications for vulnerabilities by simulating attacks — tools include OWASP ZAP, Burp Suite Enterprise, Invicti. SCA (Software Composition Analysis): Identifies vulnerable open-source dependencies and license risks — tools include Snyk, Black Duck, Dependabot, Sonatype Nexus. Furthermore, IaC Security Scanning: Scans Terraform, CloudFormation, Kubernetes manifests for misconfigurations before deployment — tools include Checkov, Terrascan, Trivy, tfsec. Additionally, Secrets Detection: Prevents credentials, API keys, and tokens from entering source control — tools include GitGuardian, TruffleHog, git-secrets. Moreover, Container and Runtime Security: Scans container images for CVEs and monitors runtime behavior — tools include Trivy, Aqua Security, Falco, Sysdig.
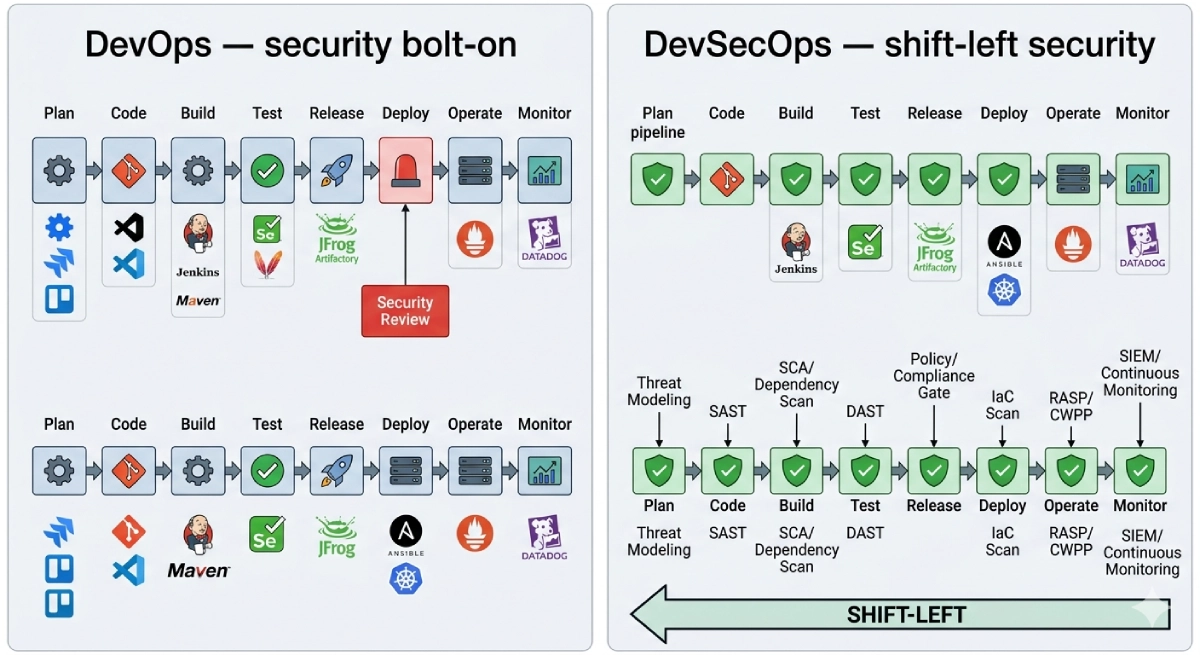
DevSecOps vs DevOps: Pipeline Architecture Deep Dive
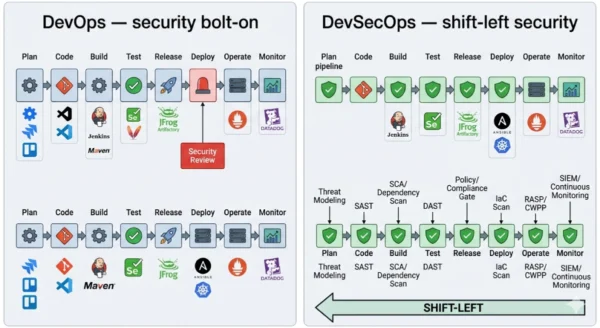
DevOps Pipeline Architecture
- Plan: Requirements and backlog — security considerations informal or absent at this stage
- Code: Developers write and commit code — no automated security scanning at commit time
- Build: CI system compiles and packages the application — dependency vulnerabilities not scanned
- Test: Automated functional and performance tests — security testing limited or manual
- Release: Manual security review gate — single point that creates bottleneck and deadline pressure to skip
- Deploy: Infrastructure provisioning and deployment — IaC misconfigurations not automatically checked
- Operate: Production monitoring — security incidents detected reactively after breach occurs
- Monitor: Performance and availability metrics — security monitoring a separate, siloed function
DevSecOps Pipeline Architecture
- Plan: Threat modeling and security requirements — STRIDE analysis, abuse case definition, security stories in backlog
- Code: SAST + secrets detection on every commit — developers get security feedback in their IDE and PR review
- Build: SCA dependency scanning + container image scanning — known CVEs blocked before artifact publication
- Test: DAST against deployed test environment — runtime vulnerability testing catches what SAST misses
- Release: Automated compliance policy gate — policy-as-code enforces security standards without manual review
- Deploy: IaC security scanning (Checkov/Terrascan) — misconfigurations caught before infrastructure provisioning
- Operate: RASP + CWPP runtime protection — active defense detects and blocks attack patterns in production
- Monitor: SIEM + continuous vulnerability management — security events correlated alongside performance signals
DevSecOps vs DevOps: The Shift-Left Security Control Map
| Pipeline Stage | DevOps Security Activity | DevSecOps Security Control | Tools (DevSecOps) |
|---|---|---|---|
| Plan | Informal — no structured security activity | Threat modeling, security user stories, abuse cases | STRIDE framework, IriusRisk, OWASP Threat Dragon |
| Code | Code review — security informal, inconsistent | SAST, secrets detection, IDE security plugins | Semgrep, SonarQube, GitGuardian, Snyk Code |
| Build | Functional tests only — no dependency scanning | SCA, container image scanning, license checks | Snyk, Black Duck, Trivy, Dependabot, Sonatype |
| Test | Functional and performance testing only | DAST, API security testing, fuzzing | OWASP ZAP, Burp Suite Enterprise, StackHawk |
| Release | Manual security review gate (bottleneck) | Policy-as-code compliance gate, automated sign-off | Open Policy Agent (OPA), Kyverno, Conftest |
| Deploy | Infrastructure provisioned without security checks | IaC scanning, CSPM, secrets manager integration | Checkov, tfsec, Terrascan, HashiCorp Vault |
| Operate | Reactive incident response after detection | RASP, CWPP, runtime container security | Aqua Security, Falco, Sysdig, Datadog Security |
| Monitor | Performance/availability metrics — security separate | SIEM, continuous vuln management, threat intel | Splunk, Elastic SIEM, Wiz, Lacework, Prisma Cloud |
DevSecOps vs DevOps: Use Cases and Adoption Scenarios
Where DevOps (Without Full DevSecOps) Remains Common
- Early-stage startups: Minimal security tooling is a pragmatic early-stage choice — shipping fast to validate the business model takes priority before security infrastructure investment is justified
- Internal tooling and low-risk applications: Tools that handle no sensitive data, have no external attack surface, and are used only by trusted internal users can operate with lighter security overhead
- Greenfield projects in low-compliance industries: Applications outside regulated industries with no PII or financial data, where the cost-benefit of full DevSecOps toolchain setup is not justified by risk profile
- Organizations in early DevOps maturity: Teams that have not yet established reliable CI/CD pipelines cannot effectively shift security left — DevOps foundation must come before DevSecOps evolution
- Rapid prototype and R&D environments: Throwaway code, internal research tooling, and experimental projects where production security standards are deliberately deferred
Where DevSecOps Is Non-Negotiable
- Regulated industries: Financial services (PCI DSS, SOX), healthcare (HIPAA), government (FedRAMP, NIST 800-53), and critical infrastructure all require demonstrable security controls at every pipeline stage
- Cloud-native applications: Microservices, containers, and serverless architectures expand the attack surface dramatically — DevSecOps provides the container scanning, IaC security, and runtime protection these environments require
- SaaS platforms handling customer data: Any application storing PII, payment information, or health records must treat security as a pipeline-level control — breach costs and regulatory fines dwarf the cost of DevSecOps implementation
- Organizations with AI-assisted development: 97% of organizations use or plan to use AI in the SDLC — AI-generated code requires the same automated security validation as human-written code, at machine speed
- Open-source and public-facing projects: High-profile attack surface, supply chain risk, and community scrutiny make automated security scanning essential — 512,000 malicious packages were discovered in open-source registries in 2024 alone
DevSecOps vs DevOps: Industry Adoption Patterns
| Industry | DevOps Maturity | DevSecOps Priority | Key Driver |
|---|---|---|---|
| Financial Services | High — fast delivery essential for competitive products | Critical — regulatory mandates and breach cost exposure | PCI DSS, SOX, breach liability ($4.88M average) |
| Healthcare | Medium — regulated pace but digital transformation accelerating | Critical — patient data protection and HIPAA compliance | HIPAA, patient data breach penalties, ransomware targeting |
| Technology / SaaS | Very high — CI/CD culture embedded | High — customer data trust and supply chain risk | Competitive differentiation, SOC 2, open-source risk |
| Government / Defense | Low-medium — slow procurement, legacy systems | Critical — national security and FedRAMP requirements | FedRAMP, NIST 800-53, CMMC for defense contractors |
| Retail / E-commerce | High — seasonal demand requires rapid deployment | High — PCI DSS, payment data, customer PII | Card data protection, fraud prevention, brand reputation |
| Startups | High — move fast culture | Medium-Low early stage, critical at scale | Investor due diligence, SOC 2 for enterprise sales |
12 Critical Differences: DevSecOps vs DevOps
The DevSecOps vs DevOps comparison below covers every key dimension — from pipeline philosophy and security integration model to team structure, tooling, compliance posture, and breach cost impact.
Aspect | DevOps | DevSecOps |
|---|---|---|
| Security Philosophy | Security as a gate — final review before release, managed by a separate security team | Security as code — automated, continuous, shared responsibility embedded at every pipeline stage |
| Security Integration Point | End of pipeline — single pre-release security review creates bottleneck and deadline skip pressure | Every stage — Plan through Monitor each has specific automated security controls and feedback mechanisms |
| Vulnerability Discovery Timing | Late — vulnerabilities found in staging or production where fix cost is $100–$1,000+ per issue | Early — SAST catches issues at commit where fix cost is $1–$10 per issue (10–1,000x cheaper) |
| Team Structure | Two teams: Dev + Ops collaborate; Security is a separate external function | Three disciplines united: Dev + Sec + Ops share ownership — security engineers embedded in delivery teams |
| Breach Cost Impact | Average $4.88M breach cost — high DevOps but low DevSecOps adoption provides no systematic cost reduction | High adopters save $1.7M per breach (IBM 2024); adding AI automation saves additional $2.2M per incident |
| Compliance Posture | Manual compliance evidence collection — labor-intensive audits, point-in-time assessments | Continuous compliance — automated policy gates produce real-time audit evidence for SOC 2, PCI DSS, GDPR, HIPAA |
| Open-Source Risk Management | No systematic SCA — vulnerable dependencies enter production through standard package managers | SCA scanning at build stage — known CVEs blocked before artifact publication, license risks flagged automatically |
| Developer Security Feedback | Delayed — security issues surfaced days or weeks after code written, context lost | Immediate — SAST and secrets detection in IDE and PR review gives developers security feedback within minutes |
| Infrastructure Security | IaC deployed without security validation — misconfigurations caught only after production incidents | IaC scanning (Checkov, tfsec) blocks misconfigured infrastructure before provisioning — CSPM monitors runtime |
| Incident Response Speed | Reactive — breach lifecycle averages 322 days (IBM 2024) without automation-assisted security | Proactive — organizations with AI and automation have 214-day breach lifecycle (108 days faster) |
| Toolchain Complexity | Lower — CI/CD, monitoring, and IaC tools; no dedicated security toolchain required | Higher — adds SAST, DAST, SCA, IaC scanner, secrets detection, container security, SIEM to DevOps toolchain |
| Deployment Frequency Impact | High — no security bottleneck but vulnerability debt accumulates in production | Equal or higher — automated security gates add minimal latency; 73% of manual security processes that slow releases are eliminated |
DevSecOps vs DevOps: Implementation Guide
Phase 1 — Foundation and Assessment (Weeks 1–2)
- Audit your current pipeline security posture: Map every CI/CD stage and identify where security activities currently occur — or don’t. Document what tools are already in place (SAST, dependency scanning, secrets detection) and what gaps exist. A simple traffic-light assessment (red/amber/green per stage) gives you a clear starting picture.
- Identify your highest-risk exposure points: Determine which applications handle sensitive data, which codebases have the most open-source dependencies, and which infrastructure environments have the weakest security controls. Prioritize DevSecOps implementation where breach impact is greatest, not where it is easiest.
- Assess team skills and cultural readiness: 45% of organizations cite skills gaps as their top barrier. Survey your developers on security knowledge, identify security champions who can bridge Dev and Sec, and assess your security team’s willingness to shift from gatekeeper to enabler. Cultural transformation is harder than tooling integration.
- Define your compliance requirements: Map the specific security controls required by your industry regulations (PCI DSS, HIPAA, SOC 2, FedRAMP) to specific pipeline stages. Compliance-driven DevSecOps has clearer ROI and stronger organizational buy-in than security-only justifications.
- Choose a pilot application: Select a single application — ideally one with active development, moderate security risk, and an engaged team — for initial DevSecOps toolchain implementation. Do not try to transform every pipeline simultaneously.
Phase 2 — Toolchain Integration (Weeks 3–8)
Immediate Wins — Start Here
- Secrets detection: Add GitGuardian or TruffleHog to your pre-commit hooks and CI pipeline — prevents credentials from entering source control. Zero false positives for high-confidence detections. Fastest DevSecOps win with immediate risk reduction.
- Dependency scanning (SCA): Enable Dependabot (GitHub) or Snyk in your repositories — automated PRs for vulnerable dependency updates with minimal configuration. Directly addresses the 81% of codebases with open-source CVEs.
- Container image scanning: Add Trivy to your CI pipeline to scan Docker images before pushing to registry — catches OS-level and application CVEs in container base images before deployment.
- SAST on PR: Add Semgrep or SonarQube as a required CI check on pull requests — gives developers security feedback in the PR review flow they already use daily.
Phase 2 Additions — Weeks 4–8
- IaC security scanning: Integrate Checkov or tfsec into Terraform and Kubernetes manifest pipelines — blocks misconfigured infrastructure before provisioning and generates compliance evidence automatically.
- DAST in test environments: Configure OWASP ZAP or StackHawk to run automated API and web application security testing in your staging environment after deployment — catches runtime vulnerabilities SAST misses.
- Policy-as-code compliance gates: Implement Open Policy Agent (OPA) or Conftest to enforce security policies at release — automated compliance sign-off replaces manual security review gates.
- Security metrics dashboard: Instrument your pipeline to track vulnerability count by severity, mean time to remediation, and false positive rate — data-driven tuning is essential for reducing friction and demonstrating ROI.
Phase 3 — Mature and Scale (Months 3–6)
- Security champions program: Identify and formally recognize 1–2 security champions per development team — engineers who receive extra security training, serve as the first line of security review, and bridge the gap between the security team and daily development work. 72% of security professionals rate organizations with security champions significantly higher on security posture.
- Threat modeling at scale: Introduce structured threat modeling (STRIDE or PASTA methodology) into sprint planning for new features — security requirements identified at design cost a fraction of post-development remediation. Use tools like IriusRisk or OWASP Threat Dragon to make this systematic rather than heroic.
- Runtime security and SIEM integration: Deploy runtime container security (Falco, Aqua) for production workloads and integrate security events into your SIEM — connects pipeline security posture with production threat detection for end-to-end visibility.
- Expand to all pipelines: Apply the toolchain and process established in your pilot to all production application pipelines — use pipeline templates in Jenkins Shared Libraries or GitHub Actions reusable workflows to enforce consistent DevSecOps controls across your entire engineering organization.
- Measure and report on security outcomes: Track and report on breach cost avoidance, vulnerability reduction rates, compliance audit efficiency, and deployment frequency impact of DevSecOps controls. Business-language metrics drive continued investment and executive support for the program.
DevSecOps vs DevOps: Cost, ROI and Breach Impact Analysis
Avg Breach Cost
$4.88M
Global average in 2024 — up 10% YoY (IBM Cost of a Data Breach 2024)
DevSecOps Saving
$1.7M
Per breach saved by high DevSecOps adoption vs no DevSecOps (IBM 2024)
AI Automation Saving
$2.2M
Additional breach cost reduction from AI and automation in security pipeline
Breach Lifecycle
108 Days
Shorter breach lifecycle with automation — 214 days vs 322 days without
Vulnerability Fix Cost: The Economic Case for Shift-Left
| SDLC Stage | Relative Fix Cost | DevOps Detection Rate | DevSecOps Detection Rate |
|---|---|---|---|
| Design / Requirements | $1 (baseline) | Rare — no formal threat modeling in most teams | High — threat modeling at planning stage is standard |
| Development / Coding | $10 | Low — code review catches some security issues informally | High — SAST + secrets detection on every commit and PR |
| Build / CI | $25 | Low — no SCA or container scanning in standard DevOps | High — SCA, container scanning, and SBOM generation automated |
| Testing / Staging | $100 | Occasional — manual pen test or pre-release security scan | Systematic — DAST, API testing, and compliance gate automated |
| Production / Post-Release | $1,000+ | Common — most vulnerabilities detected here or via breach | Rare — layered scanning catches most issues before production |
DevSecOps ROI and Performance Metrics
| Metric | DevOps (No DevSecOps) | DevSecOps | Source |
|---|---|---|---|
| Mean time to remediate vulnerabilities | Baseline | 50% faster | Industry research consensus |
| Security incidents post-adoption | Baseline | 65% fewer incidents | Aggregate DevSecOps studies |
| Critical vulnerabilities in production | Baseline | 73% fewer | DevSecOps platform research |
| Deployment frequency | Baseline | Up to 3x higher for mature teams | DORA / State of DevOps |
| Compliance audit time | Weeks of manual evidence gathering | Continuous automated evidence | GRC platform benchmarks |
| Average ROI | N/A | 300% within 2 years | DevSecOps platform research |
| Breach cost (average) | $4.88M | ~$3.18M (saving $1.7M) | IBM Cost of a Data Breach 2024 |
DevSecOps vs DevOps: Decision Framework
Choosing the Right Security Integration Model
The DevSecOps vs DevOps decision is not binary — it is a maturity spectrum. Every organization doing DevOps should be moving toward DevSecOps at a pace matched to their risk profile, compliance obligations, and team capacity. The question is not “if” but “how fast” and “where to start.” Organizations handling sensitive data, operating in regulated industries, or building at scale have no defensible reason to delay DevSecOps adoption given the breach cost and regulatory risk economics of 2026.
Remain on DevOps-First If:
- Your team has not yet established reliable CI/CD pipelines — DevOps foundation must exist before DevSecOps tools can be embedded in it
- You are pre-product, building internal prototypes, or in a pure R&D phase with no external attack surface or sensitive data handled
- Your application has zero external users, zero PII or payment data, and zero regulatory compliance obligations — security investment is genuinely not proportionate to risk
- You are in the first 90 days of a DevOps transformation — fixing broken pipelines, establishing CI/CD culture, and automating deployments takes priority over adding security tooling to broken processes
- You lack the budget for even basic DevSecOps tooling — in this case, start with free tools: Semgrep Community, Trivy, Dependabot, and git-secrets all provide meaningful security coverage at no cost
Prioritize DevSecOps Now If:
- Your application handles any customer PII, payment data, health records, or other sensitive information — breach cost exposure alone justifies DevSecOps investment
- Your industry requires SOC 2, PCI DSS, HIPAA, FedRAMP, or similar compliance certifications — continuous automated evidence collection transforms your audit process
- Your engineering team uses AI tools for code generation — AI-generated code requires the same automated security validation as human-written code and cannot be safely reviewed manually at scale
- Your codebase depends heavily on open-source packages — 81% of codebases with open-source components carry at least one high or critical vulnerability without SCA scanning to catch them
- You are scaling your engineering team or pipeline — security technical debt is exponentially harder to address at scale than at small team size; shift left now before pipeline sprawl makes it prohibitive
DevSecOps vs DevOps: Maturity Level Decision Table
| Team Maturity | Recommended Posture | Starting Point |
|---|---|---|
| No CI/CD yet | Establish DevOps first | Jenkins or GitHub Actions pipeline before any security tooling |
| Basic CI/CD (no security) | Add quick wins immediately | Secrets detection + Dependabot — zero-friction, immediate risk reduction |
| Stable CI/CD | Full DevSecOps Phase 1–2 | SAST on PR + container scanning + IaC scanning in 4–8 weeks |
| Mature DevOps | Full DevSecOps with DAST and OPA | Add DAST, policy-as-code gates, security champions, threat modeling |
| Elite DevOps | DevSecOps + AI-assisted security | AI-powered SAST, continuous compliance, SBOM generation, RASP in production |
The Hybrid Reality in 2026
No organization has perfect DevSecOps across every pipeline simultaneously. Most are in active transition — some pipelines fully instrumented, others still relying on manual reviews. The important shift is directional: every new pipeline should be built with DevSecOps controls from day one, and every existing pipeline should be progressively hardened. The DevSecOps vs DevOps distinction is less about tool installation and more about organizational culture — security as everyone’s job versus security as someone else’s problem.
Frequently Asked Questions
DevSecOps vs DevOps: Final Takeaways for 2026
The DevSecOps vs DevOps comparison ultimately comes down to where in the lifecycle your organization pays for security — and how much. Every organization pays for security: either continuously through embedded automation that catches vulnerabilities when they cost $1–$10 to fix, or episodically through breach response, regulatory fines, and emergency remediation when vulnerabilities reach production at $1,000+ each and $4.88 million per incident on average.
DevOps — Key Takeaways:
- Foundation of modern software delivery — 80% of organizations practice DevOps
- Security is a gate, not a pipeline control — single review before release
- Enables speed and collaboration but accumulates security technical debt
- 81% of teams knowingly ship vulnerable code under deadline pressure
- Average $4.88M breach cost without systematic security automation
- Prerequisite for DevSecOps — you cannot shift security left without CI/CD
DevSecOps — Key Takeaways:
- $10B market in 2026, growing to $37B by 2035 — 14% CAGR
- Security at every stage — SAST, SCA, DAST, IaC, runtime controls
- Saves $1.7M per breach; AI + automation adds $2.2M more (IBM 2024)
- 50% faster MTTR, 65% fewer incidents, 73% fewer production CVEs
- 300% average ROI within 2 years of mature implementation
- Cultural shift required — security champions and shared ownership are key
Practical Recommendation for 2026:
If your team has working CI/CD pipelines and handles any sensitive data or has any compliance obligations — start DevSecOps today with the three highest-ROI quick wins: secrets detection, dependency scanning (Dependabot or Snyk), and container image scanning (Trivy). These three tools, all available free or low-cost, can be operational in days and immediately reduce your most exploitable risks. From there, add SAST on PR review, IaC scanning, and DAST in your test environment over the following 4–8 weeks. The full cultural transformation takes longer — but the tooling foundation that makes security automated, measurable, and developer-friendly is the lever that makes the culture change tractable. In the DevSecOps vs DevOps decision in 2026, the question is not whether to move to DevSecOps — it is how quickly your team can get there.
Whether you are a student learning the principles of secure software development, a developer looking to build security into your first pipeline, or a CISO making the case for organizational investment — the DevSecOps vs DevOps comparison gives you the complete picture of what the shift requires, what it costs, and what it saves. Explore the related topics below to build out your full understanding of the modern secure delivery stack.
Related Topics Worth Exploring
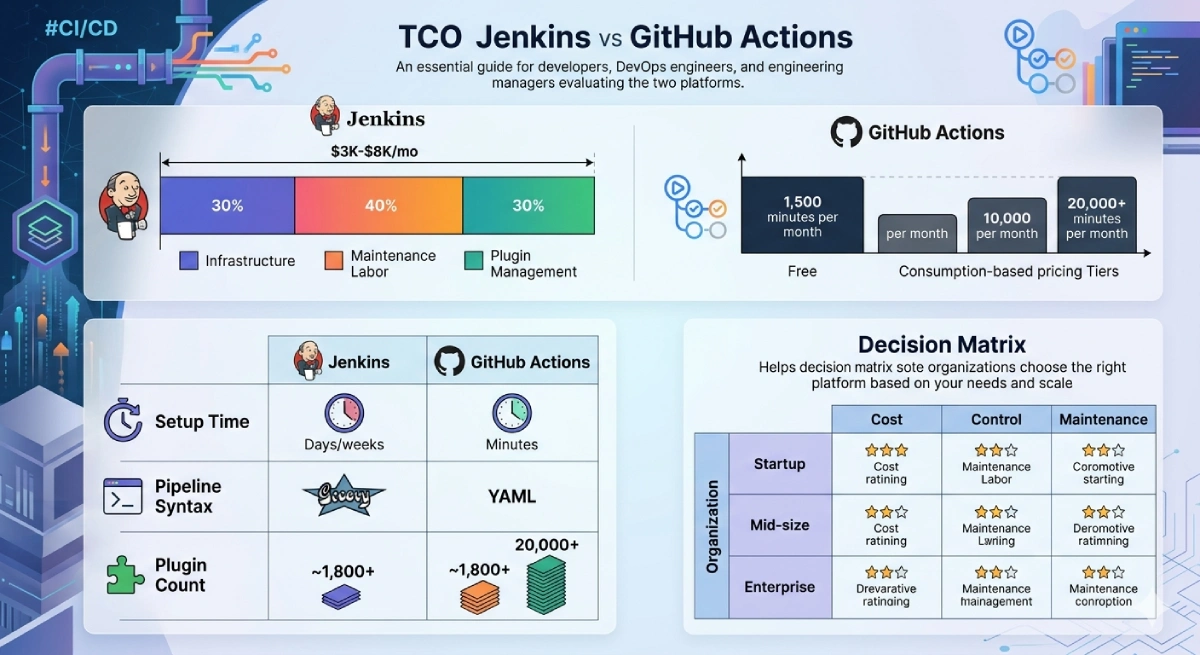
Jenkins vs GitHub Actions
The CI/CD pipeline is where DevSecOps security controls live. Explore whether Jenkins or GitHub Actions is the right foundation for embedding SAST, SCA, IaC scanning, and compliance gates into your delivery pipeline — and how each platform handles security tool integration differently.
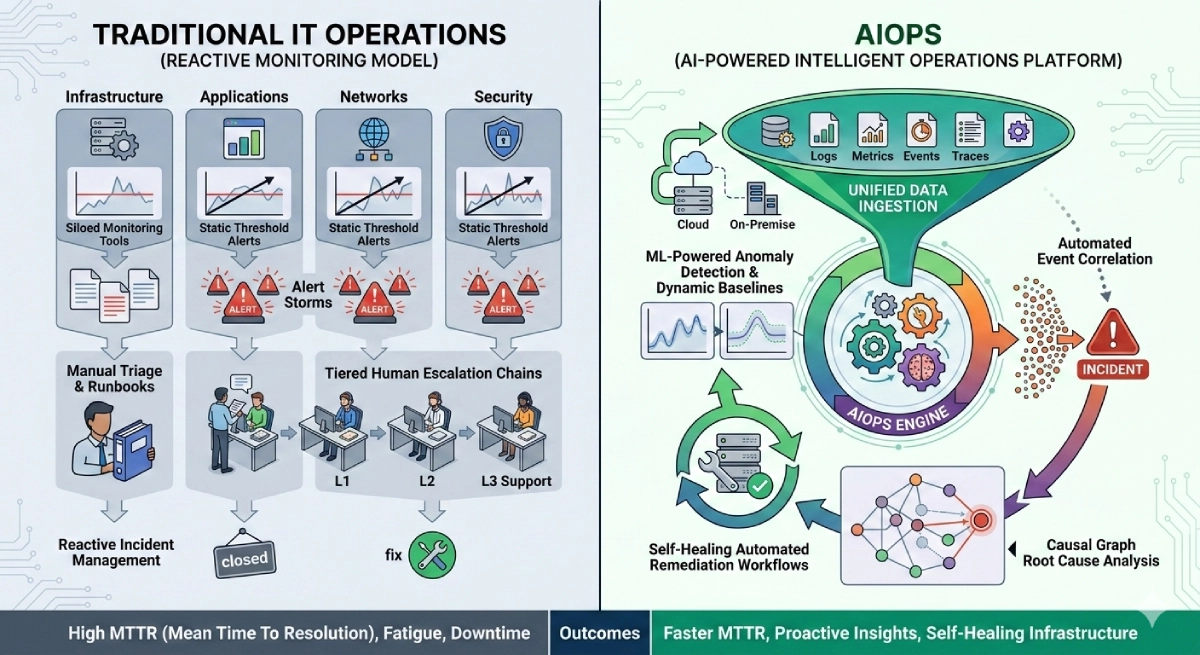
AIOps vs Traditional IT Operations
DevSecOps secures the delivery pipeline — AIOps secures and automates what happens after deployment. Understand how AI-powered operations monitoring detects anomalies, correlates security events, and enables the self-healing infrastructure that completes the secure delivery lifecycle.
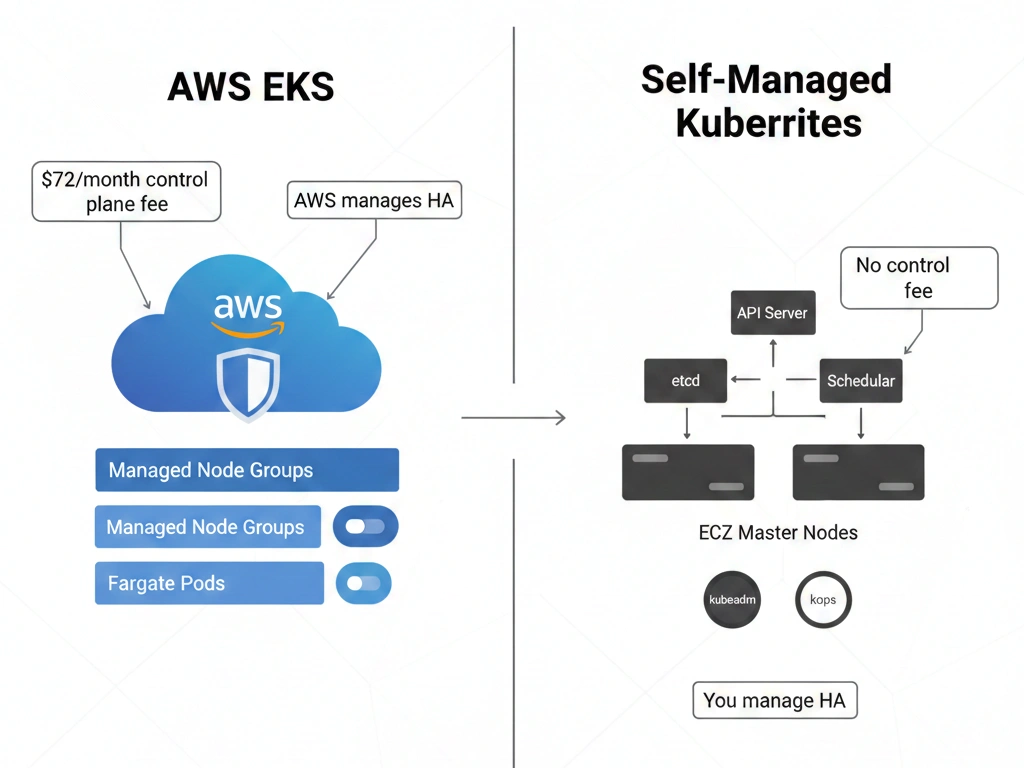
Kubernetes vs Docker Swarm
Container orchestration is the runtime environment that DevSecOps pipelines deploy to. Compare Kubernetes and Docker Swarm security posture — RBAC, network policies, pod security standards, and secrets management — to understand how your container platform choice shapes your DevSecOps architecture.